Integrate your app or make all your apps enterprise login enabled, it is super easy to get started with Whydah.
From an easy start to 40 000 logins per minute and above. Whydah can easily support millions of active user sessions.
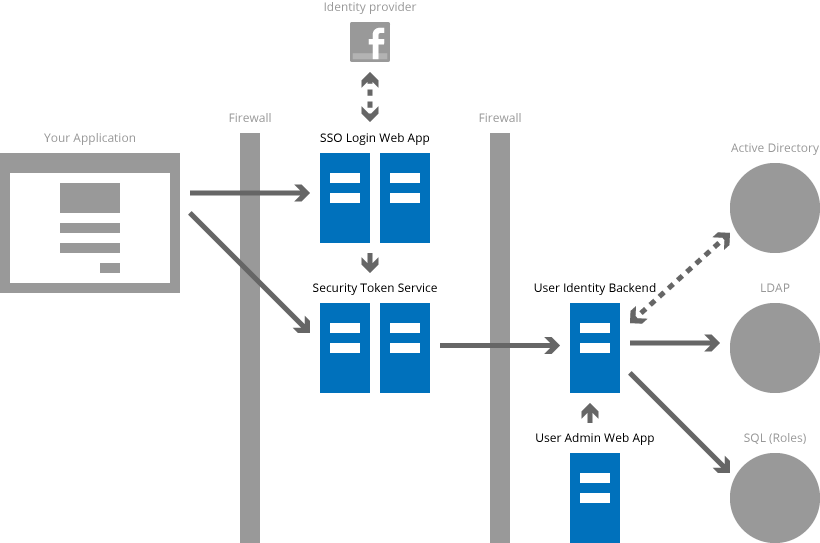
Many identity stores and external identity providers are supported. Web-applications, desktop applications and mobile phone apps.
Built to be secure with multi-layer authentication and separation of concerns to deflect common attack vectors.
Whydah is an Identity and Single Sign-On solution that provides advanced role-based access control and flexible integrations.
Security in Whydah is built around authentication and authorization. Authentication means you can be sure the user is who he claims to be, and authorisation means the user has access to what he is supposed to have access to. The user information is stored using the User Identity Backend.
A: IAM/SSO should be black-box purchases, but as commented above, today's black-box solutions keep failing in organizations by being to "different" or "difficult" for many development teams/projects. One of the reasons seems to be that developers gets confused by the massive XML-scaffolding in SAML2 tokens and the lack of development/test stand-alone deployments which easily integrate with the project CI infrastructure.
A: OpenSSO has had it's issues in the transition from Sun Microsystems to ForgeRock, especially regarding setup and administration. This is better now, but the resistance from dev-teams to integrate with SAML2 tokens is still so high that many projects still implement their own auth and user databases. Whydah was made to remove these impediments so Companies get a working IAM/SSO strategy.
A: Those products are great and full of functionality. But, and there is a but. If we look at companies which have implemented them you will find that in most companies more than 50% of their in-house developed systems do not integrate with the IAM/SSO solution, rendering the investment not very valuable. The reasons are usually/probably a combination of the ones mentioned above. IAM/SSO and testability - how to test IAM solution and what can/should be automated?
Username: pit Password: Brad
Or try the Facebook-login.
Username: admin Password: admin.
User Admin Web AppThe user database will be cleared every night, so feel free.
Read the setup recommendations and the release notes on our Wiki.
UIB is the heart and soul of Whydah, keeping your identities secure.
UAS allow fine-grained UserAdmin control for 3trd party Applications.
STS handles the tokens containing roles and properties.
SSOLoginWebApp provides a configurable whitelabeled web SSO login interface.
UAWA is the application for administrating your users.
A simple standalone CRM service to bridge users with customerdata. Can be morphed to a CRM proxy to existing CRM installations
A standalone service to record and visualize SSO/IAM usage across your whydah applications.
Support is provided as a professional service from Cantara.
Contact us at totto@cantara.no for further details.
If you want to contribute on Whydah, development, set up a development environment using the Whydah GitHub repositories and submitt pull-requests and/or join the #whydah channel on Cantara Slack.
In order to be successful with an IAM/SSO strategy, it is essential to establish a mindset about the roles used for different applications. We have seen many chaotic situations over the years. For example Active Directories with more than 1000 security groups but only 400 users using only 10 applications. Another company had over 500 applications, all with different user databases. It is quite common to leave definition of roles to the application, whydah allows to keep this practice but also regain some control. You also store and gather all roles in one place on a single identity.
This method take into consideration that you have a legacy of users to migrate. If that is not the case and you are starting from scratch (Lucky you), skip the action items related to migration. How do you get started?
We suggest creating a detailed plan on how you want to aproach this. Here is a suggested list of activities to get you started.
Whydah is agnostic to how you map your roles and identities. You may do it any way that gives meaning. The fundamental structure in whydah is illustrated below.
Whydah helped us create a common userdatabase for a dozen of custom applications used by more than 100 000 users.
Ivar IT Manager
| User field | Sample data | Comment |
|---|---|---|
| Username | Donaldduck | Avoid using e-mail adresses as they will change! |
| FirstName | Donald | The users first name, useful to Welcome the user |
| LastName | Duck | The users last name |
| donald@duckburg.com | Necessary for the user to be able to reset his PW | |
| Phone number | 99 99 99 99 | Necessary for two factor autentication (If used) |
| Customer ref | 313 | Customer ref common for all applications |
| App ID | App name | Org ID | Org name | Role name | Properties | Comment |
|---|---|---|---|---|---|---|
| 1 | ScroogeVault | 1 | MoneyBin | Employee | donald@ducksburg.com | E-mail as prop may be useful* |
| 1 | ScroogeVault | 1 | MoneyBin | Manager | no | Property "no" says that Donald not a manager in the Scrooge Vault |
| 34 | LeafApp | 314 | Nissan | CarUser | 313 | Gives the user access to administer his Leaf with reg nr 313 |
| 314 | JudgeDirectory | 1234 | Junior Woodchucks, Ducksburg | Organizer | {"orgid": "1234", "orgname": "Junior Woodchucks, Ducksburg"} | JSON stored as property for ease of integration |
| 314 | JudgeDirectory | 1235 | Junior Woodchucks, Warszaw | Organizer | {"orgid": "1235", "orgname": "Junior Woodchucks, Warszaw"} | Another organisation with access to JudgeDirectory |
| 314 | JudgeApp | 2 | Junior Woodchucks Foundation | JudgeAdmin | Poland | Admin access to JudgeDirectory for Poland |
| 314 | JudgeApp | 2 | Junior Woodchucks Foundation | JudgeAdmin | Norway | Admin access to JudgeDirectory for Norway |
*) Especially in cross domain situations or in order to map multiple users from external sources to the same user in your application